Your recent lecture at ITMO University was on hacking quantum communication systems. Yet, many sources — both scientific and popular science — state that from the point of view of modern physics, it's impossible to hack a system protected by quantum cryptography means. So, how is it possible?
Any cryptography system has particular hardware and software that realizes the encryption algorithm. For common systems, where mathematical algorithms are used to cipher information, there are two problems: both the algorithm and its realization. As computational science and capacities develop, mathematical cryptographic algorithms go out of date. Any information that has been encoded by classical cryptography algorithms can be copied and saved on disk, and read after the encryption system has been hacked. Even though new, more complex mathematical algorithms are being developed, there are many types of information that call for longlasting protection — governmental, military and commercial secrets, medical and bank records. Quantum cryptography can solve this problem, as its algorithm is generally unhackable dueto the Heisenberg indeterminacy principle. This can be easily explained: there are pairs of quantum properties, if one of them is "read", the other will be destroyed. Let's say you have a moving particle. You can assess its position in space, but then information about its speed will be lost, and vice-versa. And though you can attempt to assess its position after you measure the speed, you will get a random value. This pair of quantum properties that can't be measured simultaneously can be used for encrypting bits. If the property is chosen randomly and the cracker doesn't know which it is, he won't be able to read the information without mistakes. Still, such data transfer systems also use optical and electronic components, as well as software. So, as with any cryptographic system, we can try to find a way to hack them. This is what my research team does.
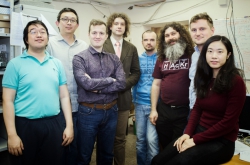
 Vadim Makarov in the quantum hacking laboratory
Vadim Makarov in the quantum hacking laboratory
How does one attack quantum cryptography systems?
We make use of flaws and imperfections of optical components. For instance, some cryptographic systems use single-photon detectors: when they absorb a photon, they register a reading. One can blind it with bright light, so that the detector stops registering readings at all. If you modulate this light in a particular manner, you can control it in such a way that it would register a reading at a particular moment. Seven years ago we showed that commercial systems used at that time could be hacked by this method. Even now, that is an issue, though the problem has almost been solved — developers have elaborated new detectors and algorithms that are resistant to these kinds of attacks. Yet, one has to admit that as opposed to mathematical cryptography, one cannot hack quantum cryptography "post factum", and such flaws do not affect the information that has already been transferred. Thus, problems related to quantum cryptography are a lot less severe.
Does resistance to hacking depend on a system's realization?
Yes. There are the so-called device independent systems; their operation is based on measuring Bell's condition and exchange of photon entanglements, while all the imperfections of detectors cannot be used in order to attack the system. Such systems have less potential problems, but are far more complex, so they are not used for commercial purposes.
 Quantum cryptography system at ITMO University
Quantum cryptography system at ITMO University
Has quantum hacking become something common? Are there any groups of hackers that specialize on these attacks, or it's done in laboratory conditions only?
There is still few quantum cryptography systems in the world, so I suppose there weren't any "wild" attacks by real crackers yet. Still, I can't guarantee that. All the methods have already been described in literature — when we find a new vulnerability, we publish an article. So, if some government would really need to hack into another's cryptographic system, that will be done. Yet, there still hasn’t been any news on quantum hacker groups in the media.
It is not hard to connect to a fiber-optic communication line: you just go down a manhole, find a cable, cut the coating and connect. As the connection is optical, you will need a small device — a fiber optic welding machine. So, if one puts some traffic cones beside the manhole, it would seem like you're doing repairs or line maintenance. There's a good chance that such attacks have already been done, but we don't know about it. And there will definitely be ones in the future, as any cryptographic system will be attacked as soon as one will use it to cipher valuable information. Cryptography was invented to protect data, after all.
 Quantum cryptography system used for data protection during the World Cup 2010.
Quantum cryptography system used for data protection during the World Cup 2010.
What is your latest research on?
We and other teams that work in this area look for new imperfections in realization and try attacking them, as this allows to understand how to deal with them. There are a lot of them, more than 20 for different systems. Since last year, my team started to collaborate with private companies on analyzing their systems — we sign a non-disclosure agreement, take all their technical documentation and look for any possible ways to hack their systems. For instance, we now collaborate with the Swiss ID Quantique Company. There is also the TOSHIBA's Research Laboratory in Great Britain, they attempt to create a system that accounts for all vulnerabilities. Those work independently, though it is hard to find vulnerabilities in your own system. That is why I never try to create my own systems, and focus on analysis only.
Is it possible to create an ideal communication security system?
With any engineering system, you can never be one hundred percent sure. You can build a hundred bridges — 99 will stand and the 100th can still fall. It's the same with cryptography: what we do is try to decrease the probability of a system being hacked. If lots of people tried attacking it and it withstood — we have some reasonable assurance that there are no serious vulnerabilities.
The modern technologies based on mathematical cryptography that we use now will once all be hacked. There are still no computers that can do it fast, but today's generation of cryptographic technologies will have to be replaced. Quantum cryptography is one of the possible options, as the algorithm is technically unhackable. Yet, it is still not clear, how will it be used: such systems call for particular hardware and an optical communication circuit. Quantum cryptography is not particularly expensive, but at first, only large companies would be able to afford it. Still, it will eventually become cheaper, and in the future, anyone would be able to use it.