Russia’s first urban quantum communication line embedded in an existing telecommunication infrastructure was launched in 2014 by the Quantum Communications company, established by the Quantum Information Centre of ITMO’s International Institute "Photonics and Optical Information Technology". In May of 2017, the same group of specialists, in collaboration with their colleagues from Kazan Quantum Center, successfully launched the first multi-node quantum network in Russia and CIS by uniting four nodes in different districts of Tatarstan’s capital.
ITMO University’s quantum network was based on a conceptually new approach - a method of single photon generation in which the signal photons are not emitted directly by a source but are generated on subcarrier frequencies, or sidebands, as a result of modulation of a carrier wave. This approach provides for several advantages, ensuring a high robustness to external effects on the communication channel and a higher capacity. The system allows to transmit quantum information over the distances exceeding 250 kilometers (the research results were published in the Optics Express journal last year).
Specialists from the Quantum Hacking Lab at the University of Waterloo, Canada, who analyzed ITMO University’s quantum network, are amongst the leading experts on attacks on quantum communication devices. For instance, the laboratory collaborates with the Swiss ID Quantique company, as well as other companies working in this field. The analysis was conducted by research associates Shihan Sajeed and Hao Qin, as well as PhD students Anqi Huang and Poompong Chaiwongkhot under the guidance of professor Vadim Makarov, the laboratory’s head.
“When we work with companies, we sign a non-disclosure agreement and get access to all the internal engineering documentation of a system. We’ve started working remotely a couple months ago. Our first step was to analyze the documents on the system that was created in ITMO University. The next stage was coming here to have the opportunity to personally communicate with the network’s engineers and developers so as to clarify additional details,” – explain Anqi Huang and Poompong Chaiwongkhot.
As Vadim Makarov adds, all of the currently existing quantum communication systems have different designs, and the protocol used at ITMO University is different from any of its counterparts. Because of this, the researchers needed more time to analyze the network’s security. Their results will serve as a basis for a report that the group plans to finish in a month’s time. The report will be given to ITMO’s specialists, who will continue to work on these issues in collaboration with experts from the University of Waterloo.
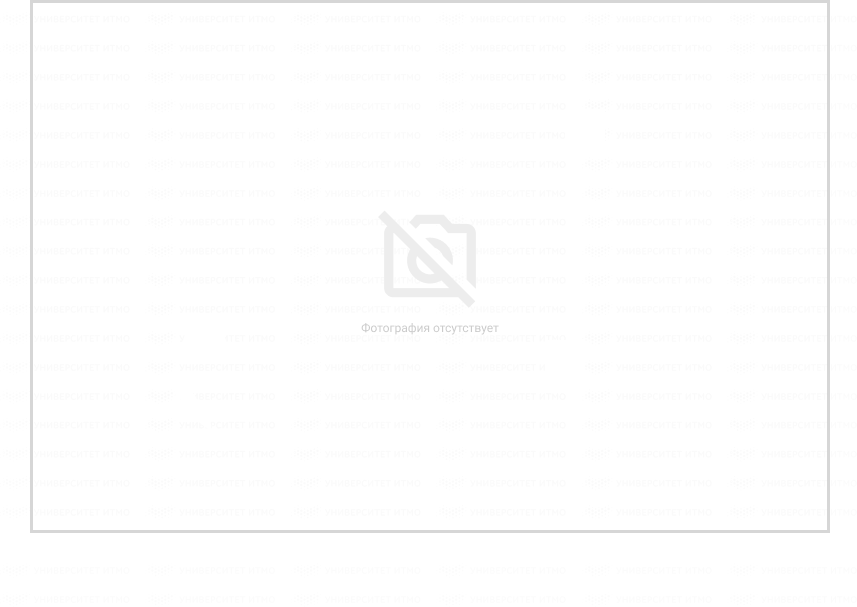
Today, it’s not enough to simply assemble a quantum network and say that it’s secure, explains Artur Gleim, head of ITMO’s Quantum Information entre.
 Artur Gleim
Artur Gleim
“It’s essential to demonstrate its reliability and security, which includes mending all of its known vulnerabilities on the hardware level. We’ve already started working on that and we are going to continue our collaboration with the Canadian specialists as well as other Russian and international groups. Our task is to create a high-quality product for the network security market, and our quantum network will play the role of a testbed for adjusting new technologies and solutions,” he says.
Quantum communications guarantee absolute impregnability of the optical communication lines to hacker attacks. As opposed to encryption algorithms, even the most complex of which can be hacked, quantum communication systems are protected by the fundamental laws of physics themselves: in their case, it is the single photons that act as information carriers, and which change irreversibly at any signal interception attempt, momentarily informing the user of the intrusion
In theory, quantum networks have no vulnerabilities, says Vadim Makarov. Despite having substantial drawbacks (being slow, having limited communication distance and requiring expensive equipment), they solve the fundamental issue of information protection: it has been rigorously proven that they are safe and can not be hacked. Another advantage is that, since the information cannot be intercepted, it also cannot be copied and stored for later decryption.
“There exist many types of information that require long-lasting protection - personal data, medical records, bank secrets, commercial, governmental, military data. Users don’t want such information to be accessed even in some 20 years time. Yet, that is exactly what mathematical cryptography is susceptible to, as one can copy the information in the form of ones and zeroes and then wait until a decryption method appears. This approach won’t do for quantum information. First of all, the protocol itself is unbreakable. Then, even if there were some vulnerabilities in hardware, one would have to assemble the equipment and hack into it the very instant it’s being transmitted, not some time later. It just doesn’t work that way. These are the two reasons why everyone’s working on quantum cryptology now,” explains Vadim Makarov.
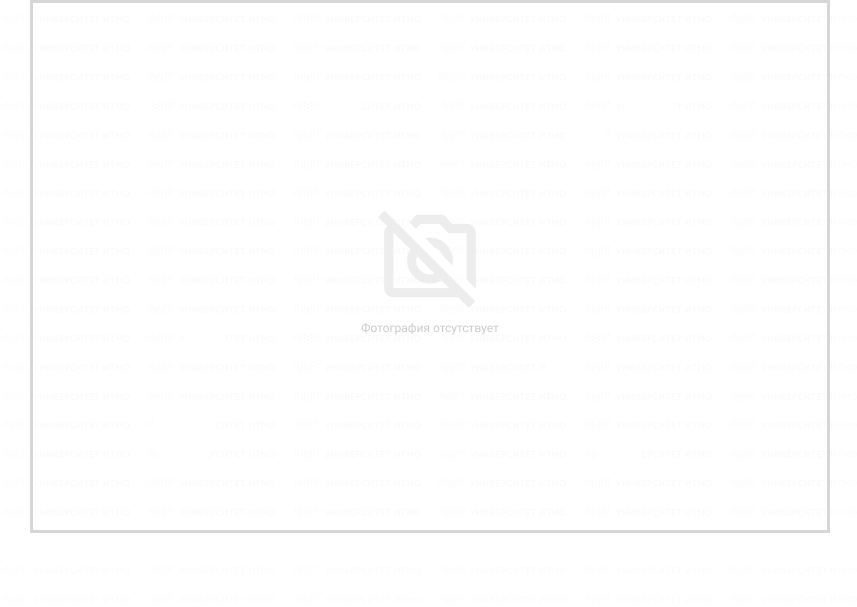
 Vadim Makarov
Vadim Makarov
Can it still be hacked?
Despite the absence of theoretical vulnerabilities, quantum networks are yet to become totally safe from hacking, which might become possible due to faults in equipment that are always present in real systems. This is what quantum cryptography has in common with its mathematical counterpart, which can also be attacked through such vulnerabilities.
“Mathematical cryptography also has many vulnerabilities, which are searched for, patched, then new methods for creating more robust systems are developed. If one analyzes the systems for long enough, they eventually develop more reliable concepts. The first designs always have some silly errors, but, in some 10-20 years, specialists find methods that are resistant to hacking. The same happens in the field of quantum cryptography, and we’re already halfway through this process. We already know enough hacking methods, there’s more than ten of them. We know how to deal with them, and we are already developing systems resistant to these methods. It’s just some engineering work to be done. In some five-ten years we can expect to have systems which we will test and say that we’ve found nothing,” comments the Head of the Quantum Hacking laboratory at the University of Waterloo.
However, as of now, specialists are still discovering new hacking methods, he adds. For instance, several years ago Vadim Makarov’s group found a serious vulnerability that had to do with “blinding” the detector. Single-photon detectors are an integral part of a quantum communication system. As they absorb a photon, they report a detection, which is the normal working mode that is essential for quantum communication algorithms. Yet, if one lights it, the detector saturates, becomes “blind” and stops seeing single photons. One can then modulate the light to take control of the detector and make it report “detections” at a pre-programmed time.
Companies are still working on this issue. Yet in laboratory conditions, it has already been solved: the scientific community has already developed a special system that is absolutely resilient to attacks on detectors. This system doesn’t have any detectors inside the secure equipment. Yet, even such attacks can not be used to copy and store encrypted information, and such vulnerabilities have no effect on the safety of the already transmitted information. Thus, systems design issues in quantum cryptography are less serious as that of the mathematical encryption algorithms.
Future of quantum networks
Massive multi-node quantum networks have already been established in the United States (Defense Advanced Research Projects Agency (DARPA)), Europe (SEQOQC), Japan (Tokyo Network, developed by the company Toshiba), as well as in China, where the world's longest-distance quantum communication system was launched.
Recent experience shows that the networks are already beginning to have customers, which in turn allows engineers to study the real experience of quantum network operation in real-world deployment. Why is this important? The use of quantum systems and logistics are quite different from those in the mathematical cryptography, says Vadim Makarov. That is why researchers today have to obtain real experience and consider solutions for the problems that system designers might face in the future.
"What could these potential problems be? The most important question is how to integrate quantum cryptography into the existing information infrastructure. After all, it has very specific uses that are very different from regular cryptography. For example, the transmission logic of the keys: you should always have a chain of optical lines, — says Vadim Makarov. — Researchers are currently working with engineers and information security specialists in order to understand how to integrate quantum methods within the already existing and wide range of methods used in classical cryptography, how to gradually introduce them and make it “painless”. Integrating quantum methods with already existing ones is a gradual process."
Still, it is unlikely that quantum principles will completely replace classical cryptography: most likely, the market will be divided between these technologies, he suggests. Despite its limited security, mathematical cryptography will still be applied in certain areas, for example for protecting information which only needs to stay confidential for a limited time. Quantum methods, on the other hand, will find a niche in areas where users need more long-term protection of confidential information.
Can vulnerabilities be eradicated completely?
They may, and such work is already underway, says Vadim Makarov. The field of quantum cryptography is still quite young: commercial systems appeared on the market only 12 years ago, while the field of science itself is about 25 years old. In order to fully guarantee security, more work still as to be done.
In classical cryptography, which has been around for much longer, certification standards appeared gradually. Today, almost every developed country has its own national laboratories which are able, in accordance with these standards, to access the product made by developers and certify that it is devoid of flaws. Thus in classical cryptography we have an established ecosystem of standardization and certification, in national and commercial laboratories. Quantum communication is now going down this path.
“Certification standards are already being developed. All main players in quantum cryptography work on them in the European Telecommunications Standards Institute (ETSI). Perhaps ITMO University will also join the efforts next year – we are already discussing this possibility”, says Vadim Makarov.
According to his estimates, it may take several years to develop a standard – and just as much time is needed to create a national laboratory. Therefore, a standardization ecosystem may appear in roughly five years.